W69 has long been a/served as/remained an intriguing/fascinating/mysterious enigma, beckoning/luring/enticing researchers and hobbyists/enthusiasts/curious minds alike. Its origins/The story behind it/How it came to be are shrouded in secrecy/mystery/unanswered questions, fueling countless theories/speculation/imaginative conjecture. Some believe/suggest/posit it is a forgotten code/ancient artifact/sophisticated puzzle, while others view it as a glimpse into the future/an anomaly/evidence of something beyond our comprehension.
- Despite/In spite of/Regardless of the lack of concrete answers/solutions/clues, W69 continues to captivate/intrigue/inspire those who seek/strive for/attempt to understand its secrets/inner workings/true meaning.
- {Perhaps one day,/Maybe someday/, /Through continued research we will finally unlock/decode/unravel the mysteries of W69.
Inside the World of W69 {
W69 is more than just a chatroom; it's a sprawling realm where anonymity reigns supreme and anything goes. Here, personas from across the globe gather to broadcast their thoughts, engage in intense debates, and explore the forbidden depths of human expression. From {philosophical{ discussions to authentic confessions, W69 offers a glimpse into the underbelly of the online world.
The atmosphere is often described as electric, fueled by a constant stream of posts that flow across the platform. Newcomers are often quickly drawn into the maze of conversation, finding themselves engulfed by the unpredictability that defines W69.
Unveiling W69
W69 is a mysterious protocol that has intrigued cryptographers, as well as. This article delves into the intricacies of W69, shedding light on its {history, structure, and potential applications|. It's designed for both beginners and cryptography, offering clear explanations and practical insights. Let's embark on this journey to unravel W69 together.
- Let's start with the origins of W69, tracing its roots back to the early days of cryptography.
- Next, we'll dive into the structural components of W69, key generation processes.
- The article concludes with potential applications of W69 in diverse areas such as cybersecurity, communication, and data security.
W69 Explained: History, Features, and Implications
W69 has risen as a potent kc9 com force in the realm of. Tracing its past reveals a complex tale of innovation. W69's distinctive features enable it to revolutionize various fields, fueling both enthusiasm and debate.
The effects of W69 are far-reaching, arguably altering the global landscape. Understanding its potential is crucial for embracing the times ahead.
Harnessing the Potential of W69: Applications and Implications
W69 is rapidly emerging as a transformative technology with widespread applications across numerous domains. Its unique attributes offer exceptional capabilities, unlocking solutions to challenging problems. From improving communication networks to driving scientific discoveries, W69 has the potential to reshape our world in unforeseen ways. The future of W69 is filled with possibilities, and ongoing research advances to harness its full potential for the benefit of humanity.
Exploring the Unknown Territories of W69
Embarking on a expedition into the uncharted territories of W69 is a daunting endeavor. Hidden in mystery, this region beckons explorers with its prospect of revelations. The landscape is harsh, posing obstacles to even the most experienced adventurers. Legends circulate about forgotten civilizations and unexplained phenomena, fueling the ambition to unravel W69's riddles.
 Kelly McGillis Then & Now!
Kelly McGillis Then & Now! Charlie Korsmo Then & Now!
Charlie Korsmo Then & Now!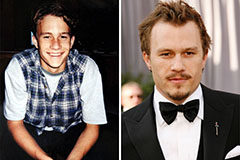 Heath Ledger Then & Now!
Heath Ledger Then & Now! Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Christy Canyon Then & Now!
Christy Canyon Then & Now!